Summary:
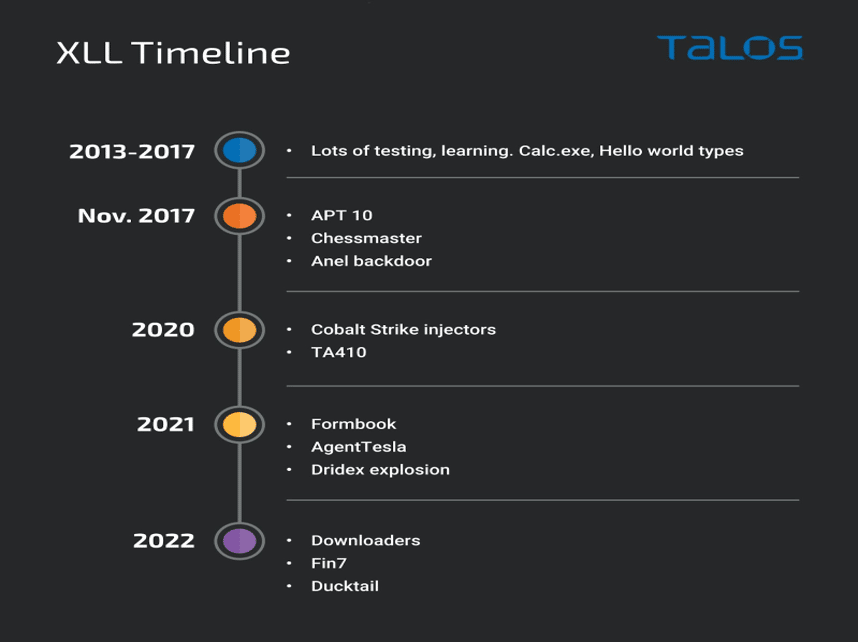
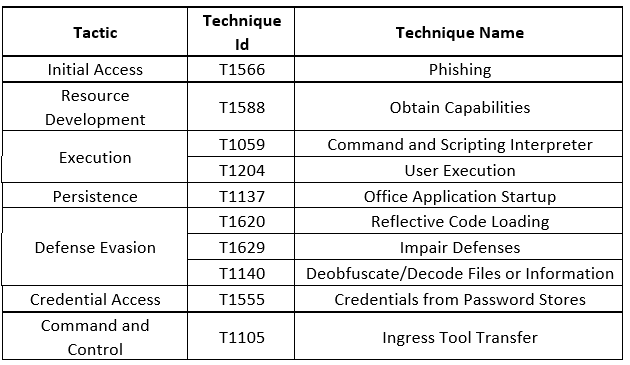
According to researchers, Excel add-in (.XLL) files are becoming more frequently used as an initial infiltration vector by threat actors.In recent months, various threat actors have improved their attack chains as a result of Microsoft's decision to restrict Visual Basic for Applications (VBA) macros by default. VBA enables non-programmers to record, create, and edit macros that can automate tasks in Office applications. Cybercriminal are trying to execute malicious code using weaponised documents delivered via spear-phishing emails and other social engineering techniques. These documents request the victims to enable macros in order to view perfectly harmless material, only to trigger the malware's stealthy background execution. Microsoft's prohibitions on macros executing in files downloaded from the internet do not apply to Publisher files, allowing attackers to take advantage of this for phishing activities.[/subscribe_to_unlock_form]
Summary:
According to researchers, Excel add-in (.XLL) files are becoming more frequently used as an initial infiltration vector by threat actors.In recent months, various threat actors have improved their attack chains as a result of Microsoft's decision to restrict Visual Basic for Applications (VBA) macros by default. VBA enables non-programmers to record, create, and edit macros that can automate tasks in Office applications. Cybercriminal are trying to execute malicious code using weaponised documents delivered via spear-phishing emails and other social engineering techniques. These documents request the victims to enable macros in order to view perfectly harmless material, only to trigger the malware's stealthy background execution. Microsoft's prohibitions on macros executing in files downloaded from the internet do not apply to Publisher files, allowing attackers to take advantage of this for phishing activities.[emaillocker id="1283"]
Threat Profile:
References:
The following reports contain further technical details:
https://thehackernews.com/2022/12/apt-hackers-turn-to-malicious-excel-add.html
[/emaillocker]