| Summary: |
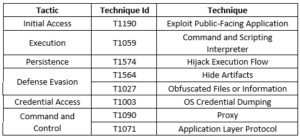
An advanced iteration of the MATA backdoor framework was detected. The targets of these attacks were primarily within the oil and gas sector and the defense industry in Eastern Europe. The attackers utilized spear-phishing emails to trick their victims into downloading malicious executables. These executables took advantage of a well-known vulnerability (CVE-2021-26411) in Internet Explorer to kickstart the infection process. This updated version of the MATA framework, which bears similarities to previous versions associated with specific threat actors, comprises a loader, a primary trojan, and an infostealer. This combination allows the malware to create backdoors and maintain a persistent presence within compromised networks. Notably, the attackers managed to breach security compliance solutions and exploit their vulnerabilities to spread the malware throughout the entire corporate network.
 [/subscribe_to_unlock_form]
[/subscribe_to_unlock_form]
| Summary: |
An advanced iteration of the MATA backdoor framework was detected. The targets of these attacks were primarily within the oil and gas sector and the defense industry in Eastern Europe. The attackers utilized spear-phishing emails to trick their victims into downloading malicious executables. These executables took advantage of a well-known vulnerability (CVE-2021-26411) in Internet Explorer to kickstart the infection process. This updated version of the MATA framework, which bears similarities to previous versions associated with specific threat actors, comprises a loader, a primary trojan, and an infostealer. This combination allows the malware to create backdoors and maintain a persistent presence within compromised networks. Notably, the attackers managed to breach security compliance solutions and exploit their vulnerabilities to spread the malware throughout the entire corporate network.
 [emaillocker id="1283"]
[emaillocker id="1283"]
Execution Flow
In these attacks, the adversaries extended their reach from a single domain controller on a production plant to encompass the entire corporate network. They exploited their access to two security solution admin panels – one for endpoint protection and one for compliance checks – to conduct surveillance on the organization's infrastructure and distribute malware to its subsidiaries. Additionally, when Linux servers were targeted, the attackers employed a Linux variant of MATA resembling the third generation of its Windows counterpart. This escalating threat involves multiple versions of MATA, including one evolved from previous iterations, 'MataDoor,' and a completely new variant (v5) in DLL form with extensive remote-control capabilities and support for various protocols.
This evolving MATA malware now features 23 commands, facilitating actions such as connectivity setup, implant management, and data retrieval. Moreover, the attackers employ additional plugins to execute 75 other commands, encompassing information gathering, process management, file manipulation, network reconnaissance, proxy functionality, and remote shell execution. Furthermore, they introduced a module allowing the use of removable storage media, like USB drives, to infect air-gapped systems. Additionally, various stealers capture sensitive data, while tools like 'CallbackHell' enable bypassing endpoint security tools by altering kernel memory and targeting specific callback routines. If this method fails, the attackers resort to documented Bring Your Own Vulnerable Driver (BYOVD) techniques.
While past instances of MATA have been associated with specific threat actors, the attribution for this recent activity remains unclear, as the newer MATA variants and techniques closely resemble those of other sophisticated APT groups. The deployment of multiple malware frameworks and MATA versions in a single attack signifies a well-resourced and highly capable threat actor. Organizations should remain vigilant, regularly update their security measures, and stay informed about emerging threats to safeguard their networks and sensitive data from these evolving and persistent adversaries.
| Threat Profile: |
| References:
The following reports contain further technical details: |