Summary:
Various threat actors, including affiliates of the LockBit ransomware group, are actively exploiting a critical security vulnerability in Citrix NetScaler ADC and Gateway appliances. This flaw, known as Citrix Bleed CVE-2023-4966 allows attackers to bypass password requirements and multifactor authentication, enabling session hijacking of legitimate user sessions. The compromise of these sessions grants malicious actors elevated permissions, facilitating the harvesting of credentials, lateral movement, and unauthorized access to data and resources.[/subscribe_to_unlock_form]
Summary:
Various threat actors, including affiliates of the LockBit ransomware group, are actively exploiting a critical security vulnerability in Citrix NetScaler ADC and Gateway appliances. This flaw, known as Citrix Bleed CVE-2023-4966 allows attackers to bypass password requirements and multifactor authentication, enabling session hijacking of legitimate user sessions. The compromise of these sessions grants malicious actors elevated permissions, facilitating the harvesting of credentials, lateral movement, and unauthorized access to data and resources.[emaillocker id="1283"]
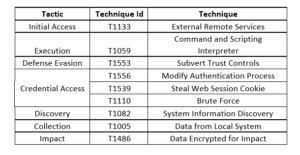
While Citrix addressed the vulnerability last month, it was already being exploited as a zero-day since at least August 2023. The vulnerability poses a significant risk, with a CVSS score of 9.4. LockBit has been observed utilizing the flaw to execute PowerShell scripts and deploy remote management and monitoring (RMM) tools such as AnyDesk and Splashtop for further actions. This revelation reinforces the persistent threat posed by vulnerabilities in exposed services, serving as a primary entry point for ransomware attacks.
The active exploitation of the Citrix Bleed vulnerability by threat actors, including LockBit affiliates, poses a severe risk to organizations. The compromise of authentication mechanisms and the potential for session hijacking underline the critical importance of promptly patching and securing exposed services to mitigate the risk of unauthorized access and ransomware attacks.
Recommendations:
We strongly recommend urge affected customers of NetScaler ADC and NetScaler Gateway install the relevant updated versions as soon as possible.
Threat Profile:
References:
The following reports contain further technical details:
https://thehackernews.com/2023/11/lockbit-ransomware-exploiting-critical.html
[/emaillocker]