Summary:
A ransomware operation termed Lorenz first observed in Feb 2021, believed to be a rebranding of the sZ40 ransomware that was discovered in Oct 2020. It is said that Lorenz ransomware gang may have link to the ThunderCrypt group. Like other ransomwares Lorenz breaches a network and can spread laterally as a result, operators gain access to the devices, in this process the hackers steal unencrypted files from servers and machines. Now in recent campaigns the Lorenz ransomware gang is using a critical vulnerability in Mitel MiVoice VOIP appliances to breach companies using their phone systems for initial access to their network. The ransomware group is exploiting the CVE-2022-29499 bug in VoIP which allows remote code execution because of incorrect data validation for this purpose. Since the Lorenz group customizes the attack for each target, it is observed that different binaries of Lorenz exist that have different behaviour. This also means that the Lorenz group continues to update the ransomware, even if it is required to create frequent changes to its code.[/subscribe_to_unlock_form]
Summary:
A ransomware operation termed Lorenz first observed in Feb 2021, believed to be a rebranding of the sZ40 ransomware that was discovered in Oct 2020. It is said that Lorenz ransomware gang may have link to the ThunderCrypt group. Like other ransomwares Lorenz breaches a network and can spread laterally as a result, operators gain access to the devices, in this process the hackers steal unencrypted files from servers and machines. Now in recent campaigns the Lorenz ransomware gang is using a critical vulnerability in Mitel MiVoice VOIP appliances to breach companies using their phone systems for initial access to their network. The ransomware group is exploiting the CVE-2022-29499 bug in VoIP which allows remote code execution because of incorrect data validation for this purpose. Since the Lorenz group customizes the attack for each target, it is observed that different binaries of Lorenz exist that have different behaviour. This also means that the Lorenz group continues to update the ransomware, even if it is required to create frequent changes to its code.[emaillocker id="1283"]
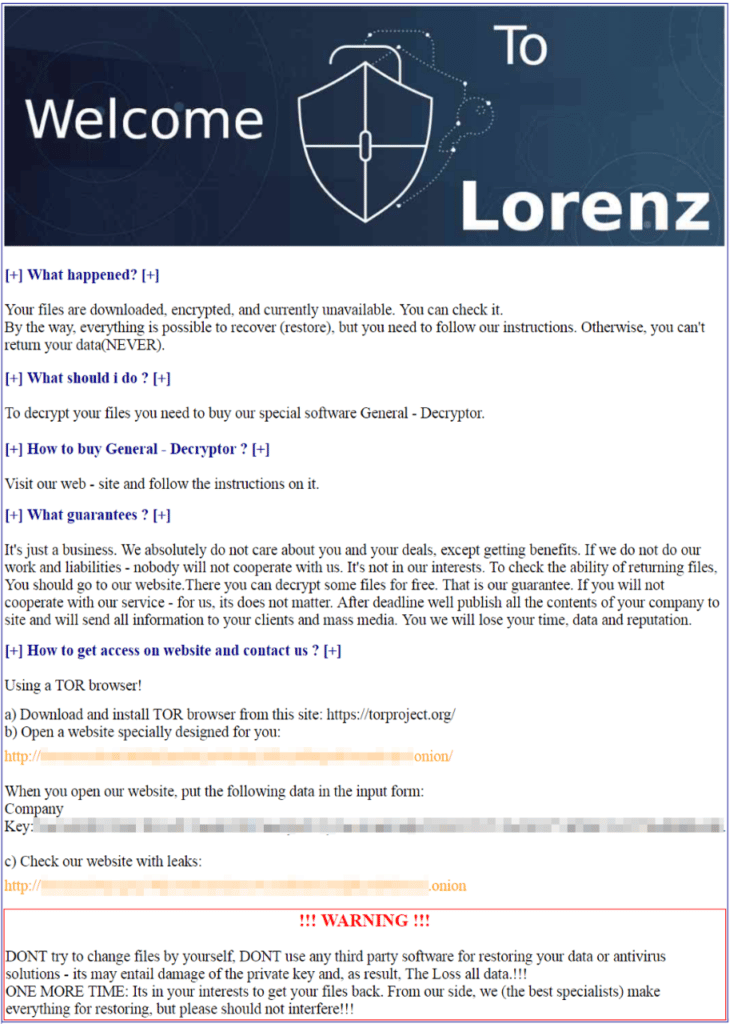
Ransom Note
References:
The following reports contain further technical details:
https://arcticwolf.com/resources/blog/lorenz-ransomware-chiseling-in/
[/emaillocker]