Summary:
Over the past few months, the majority of malvertising campaigns have primarily targeted Windows users, unsurprising given Microsoft's significant market share in the desktop and laptop computer space. However, a recent campaign has taken a different approach, focusing on both Windows and Mac users, featuring an updated version of the increasingly popular Atomic Stealer (AMOS) for Mac. Initially introduced in April 2023, AMOS was advertised as a Mac OS stealer with a specific emphasis on cryptocurrency assets. Its capabilities include harvesting passwords from browsers, accessing Apple's keychain, and featuring a file grabber. The developer has actively maintained and improved the tool, releasing a new version at the end of June.[/subscribe_to_unlock_form]
Summary:
Over the past few months, the majority of malvertising campaigns have primarily targeted Windows users, unsurprising given Microsoft's significant market share in the desktop and laptop computer space. However, a recent campaign has taken a different approach, focusing on both Windows and Mac users, featuring an updated version of the increasingly popular Atomic Stealer (AMOS) for Mac. Initially introduced in April 2023, AMOS was advertised as a Mac OS stealer with a specific emphasis on cryptocurrency assets. Its capabilities include harvesting passwords from browsers, accessing Apple's keychain, and featuring a file grabber. The developer has actively maintained and improved the tool, releasing a new version at the end of June.[emaillocker id="1283"]
Criminals acquiring this toolkit have been distributing it primarily through cracked software downloads, but they are also employing tactics such as impersonating legitimate websites and utilizing ads on popular search engines like Google to ensnare victims. This report delves into a campaign targeting TradingView, a widely used platform and app for tracking financial markets. When users seek to download a new program, they typically turn to Google for a search. Threat actors exploit this behavior by purchasing ads that mimic well-known brands, tricking victims into visiting their sites, which appear deceptively similar to official pages. For instance, an ad for TradingView uses special font characters in the domain name, seemingly attempting to evade Google's ad quality checks.
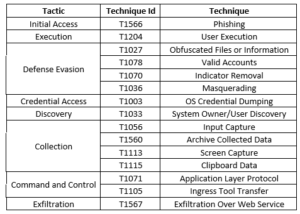
Upon clicking the ad, users are redirected to a phishing page hosted at the domain. which closely resembles the authentic TradingView website. The phishing site offers download buttons for Windows, Mac, and Linux versions of the program. A potential indicator of phishing is the site's creation date, which, in this case, was only a few days prior. Both the Windows and Linux download buttons lead to an MSIX installer hosted on Discord, which drops the NetSupport RAT (Remote Access Trojan). The downloaded "TradingView.dmg" file provides instructions on bypassing GateKeeper. Unlike regular apps, it does not need to be copied into the Mac's Apps folder but is mounted and executed. The malware is bundled in an ad-hoc signed app, making it immune to Apple certificate revocation. It persistently prompts users for their passwords until they relent and enter them.
The attacker's objective is to run their program, steal data from victims, and promptly exfiltrate it to their own server. The stolen data includes sensitive information such as passwords and cryptocurrency assets. Effective malvertising campaigns continue to exploit users' trust in search engines, combining malicious ads with convincing phishing pages. Mac malware, though less detected than its Windows counterparts, is a real threat. AMOS is designed to evade detection. Before downloading any new software, it's crucial to verify its origins. If you encounter an ad prompting a download, consider revisiting the official website directly or verifying the site's authenticity.
Threat Profile:
References:
The following reports contain further technical details:
https://thehackernews.com/2023/09/mac-users-beware-malvertising-campaign.html
[/emaillocker]