Summary:
Researchers issued an alert regarding a significant cyber threat exploiting vulnerabilities in ManageEngine ADSelfService Plus, a self-service password management and single sign-on solution. The threat involved advanced persistent threat (APT) actors deploying webshells, such as Godzilla, and other tools like NGLite and KdcSponge. The attackers exploited CVE-2021-40539, targeting at least nine global entities across diverse industries. Godzilla, a versatile webshell developed with Chinese instructions, allowed attackers to execute dynamic, potentially malicious code. NGLite, an open-source backdoor, utilized a unique communication channel based on blockchain technology, specifically New Kind of Network (NKN). KdcSponge, a novel credential-stealing tool, targeted domain controllers to extract usernames and passwords. The attackers aimed to maintain persistent access, exfiltrate sensitive information, and ultimately steal credentials. While attribution is ongoing, there were correlations with tactics employed by Threat Group 3390 (TG-3390, Emissary Panda, APT27.[/subscribe_to_unlock_form]
Summary:
Researchers issued an alert regarding a significant cyber threat exploiting vulnerabilities in ManageEngine ADSelfService Plus, a self-service password management and single sign-on solution. The threat involved advanced persistent threat (APT) actors deploying webshells, such as Godzilla, and other tools like NGLite and KdcSponge. The attackers exploited CVE-2021-40539, targeting at least nine global entities across diverse industries. Godzilla, a versatile webshell developed with Chinese instructions, allowed attackers to execute dynamic, potentially malicious code. NGLite, an open-source backdoor, utilized a unique communication channel based on blockchain technology, specifically New Kind of Network (NKN). KdcSponge, a novel credential-stealing tool, targeted domain controllers to extract usernames and passwords. The attackers aimed to maintain persistent access, exfiltrate sensitive information, and ultimately steal credentials. While attribution is ongoing, there were correlations with tactics employed by Threat Group 3390 (TG-3390, Emissary Panda, APT27.[emaillocker id="1283"]
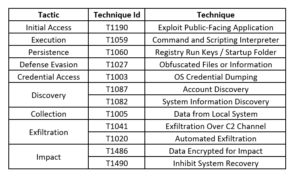
The primary vulnerability exploited in this campaign was identified as CVE-2021-40539, allowing REST API authentication bypass in vulnerable ManageEngine ADSelfService Plus instances. The attackers-initiated scanning, targeting at least 370 Zoho ManageEngine servers in the United States. Exploitation attempts leading to successful compromises in technology, defense, healthcare, energy, and education sectors. The threat actors deployed Godzilla webshell consistently across victims, with additional tools like NGLite and KdcSponge observed in a subset of compromised organizations. Godzilla, known for its rich functionality, used AES encryption for network traffic and avoided detection. NGLite leveraged NKN infrastructure for C2 communications, providing anonymity, and KdcSponge acted as a credential-stealing tool against domain controllers. The attackers demonstrated post-exploitation activities involving lateral movement, exfiltration of sensitive files, and deployment of multi-faceted tools for maintaining access.
The attack campaign exploiting CVE-2021-40539 against ManageEngine ADSelfService Plus revealed a sophisticated and well-coordinated effort by threat actors. The combination of Godzilla webshell, NGLite backdoor, and KdcSponge credential-stealing tool showcased diverse functionalities aimed at persistent network access and sensitive data exfiltration. While attribution remains ongoing, the similarities with the tactics of Threat Group 3390 suggest potential connections. This incident underscores the critical importance of timely patching, robust cybersecurity defenses, and proactive monitoring to detect and mitigate evolving cyber threats.
Recommendations:
Threat Profile:
References:
The following reports contain further technical details:
https://unit42.paloaltonetworks.com/manageengine-godzilla-nglite-kdcsponge/
[/emaillocker]